Enterprise-Grade Security.
Zero Compromises.
Security isn't a feature in TenzoShare — it's the foundation. Every layer of the stack is hardened with industry best practices, from password hashing to network isolation.
Argon2id Hashing
Memory-hard hashing with time=1, mem=64MB, threads=4, keylen=32 plus a server-side pepper stored as an environment variable.
RS256 JWT
2048-bit RSA key pair. Access tokens expire in 15 minutes. Refresh tokens valid for 7 days. JTI revocation via Redis blacklist — logout and password change both invalidate the current token.
TOTP MFA
Time-based One-Time Passwords via pquerna/otp. Full setup, verify, enable, and disable lifecycle. Compatible with any TOTP app (Google Authenticator, Authy, etc.).
RBAC — Role-Based Access
Four built-in roles with fine-grained permissions enforced at every API endpoint.
Account Lockout
Automatic account lockout after N failed login attempts. Tracks failed_login_attempts and locked_until in the database.
API Key Management
SHA-256 hashed keys stored in the database. Raw key returned exactly once at creation time. Only the key prefix is shown in listings — never the full secret.
AES-256-GCM Encryption
Every file is encrypted on upload using AES-256 in Galois/Counter Mode. A cryptographically random 12-byte nonce is prepended to each ciphertext. Decryption happens transparently at download time — no manual key management for users.
ciphertext = AES-256-GCM(plaintext, key, nonce=random(12))
stored = nonce || ciphertext
key = derived from master key per-file
TLS 1.3 Minimum
All API and web traffic enforced at TLS 1.3+. Optional mTLS available for inter-service communication between containers.
Browser-Safe Tokens
Short-lived HS256 tokens for browser downloads. 15-minute expiry. No Authorization header needed for file delivery.
5 login attempts per 15 minutes, per IP address. Redis INCR with TTL.
10 registration requests per hour, per IP. Prevents mass account creation.
5 password reset requests per hour, per IP. Prevents enumeration attacks.
10 guest file uploads per hour, per IP. Prevents abuse of anonymous sharing.
100 requests per minute per authenticated user, system-wide.
1,000 requests per minute per IP address across all endpoints.
Applied on All API Services & Nginx
Every response from TenzoShare includes a comprehensive set of security headers that protect against clickjacking, MIME sniffing, XSS, and information leakage.
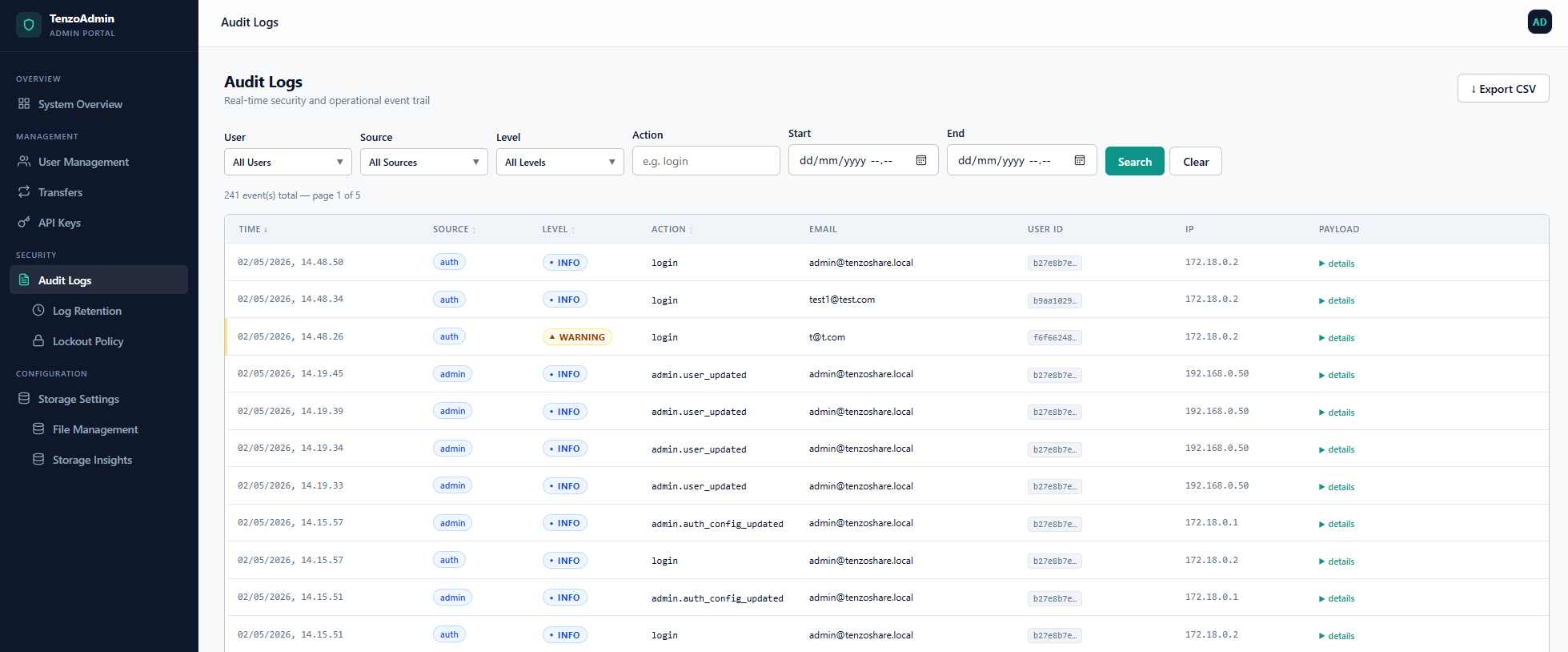
CORS_ALLOWED_ORIGINSImmutable Audit Trail
Every action in TenzoShare is recorded in an append-only, structured JSON audit log. The log is cryptographically tamper-evident and partitioned by date for efficient querying.
{
"id": "01HX7K...",
"timestamp": "2026-05-02T14:23:11Z",
"event": "file.download",
"actor": "user:alice",
"resource": "file:Q9r3x...",
"ip": "203.0.113.42",
"user_agent": "Mozilla/5.0...",
"geo": "DE, Berlin",
"result": "success",
"retention_until": "2033-05-02"
}
Traefik v3 Gateway
TLS termination, intelligent routing, rate limiting, and health-check gating. Only the gateway is exposed externally.
Docker Network Isolation
All services communicate on an isolated Docker network. No service is directly reachable from outside the host.
gRPC Inter-Service
No cross-service database queries. Data access only via gRPC. Eliminates lateral movement if one service is compromised.
Admin API Isolation
Admin APIs are only accessible with an admin role JWT. Enforced by middleware.
Want a security review?
Our enterprise support includes a dedicated security onboarding, compliance review, and direct access to the core team.